 Your new post is loading...
 Your new post is loading...
For a very long time, Apple and its pseudo-religious user-base prided itself on being a platform free of malware; those days are inarguably and unequivocally over. Its emergence as the early winner...

|
Scooped by
Gust MEES
|
Nutzer von Apple-Computern sind derzeit im Visier von Cyber-Kriminellen. Wie "Malwarebytes" berichtet, läuft aktuell eine Kampagne unter dem Namen ClearFake. Dabei soll Schadsoftware auf den Rechnern der Opfer installiert werden.
Die Betrüger tarnen die Malware dabei als Update für die Browser Safari und Chrome. Diese angeblichen Updates werden auf bereits kompromittierten Websites angeboten. Wenn man der Installation zustimmt, wird aber keine Browseraktualisierung heruntergeladen, sondern die Malware. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Apple released security updates for older iPhones to fix a zero-day vulnerability tracked as CVE-2023-41064 that was actively exploited to infect iOS devices with NSO's Pegasus spyware.
CVE-2023-31064 is a remote code execution flaw that is exploited by sending maliciously crafted images via iMessage. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Der Sicherheitsforscher Patrick Wardle machte auf der Defcon-Hackerkonferenz in Las Vegas auf mehrere Schwachstellen im Background-Task-Management (BTM) von macOS aufmerksam. Wie aus einem Bericht von Wired hervorgeht, soll es Angreifern damit möglich sein, Apples Warnsystem zu umgehen und so eine persistente Schadsoftware auf einem Mac zu installieren, ohne dass der Benutzer dies mitbekommt. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Microsoft hat eine kritische Sicherheitslücke im macOS entdeckt, die Hackern leichten Zugang zu den wichtigsten Daten Ihres Macs ermöglichen könnte. Die als "Migraine" bezeichnete Sicherheitslücke zeigt, warum es äußerst wichtig ist, Ihren Mac so schnell wie möglich zu aktualisieren.
"Migraine" ist deshalb so gefährlich, weil sie den System Integrity Protection (SIP) von Apple umgehen kann. SIP wird standardmäßig auf modernen Macs aktiviert und schützt sensible Teile des Computers vor externen Eingriffen.
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
This is new. For the very first time, Apple has released a Rapid Security Response (RSR) update to iPhone users, with a corresponding RSR for the Mac. It represents a change in how Apple will launch smaller updates—as indicated by the number of this one. After iOS 16.4.1, you might legitimately have expected iOS 16.4.2 as the small update before iOS 16.5 lands.
But no, we now have a letter, and even parentheses, to attach to the numbers: here comes Apple iOS 16.4.1 (a). Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Über manipulierte Kalendereinträge konnten Angreifer inzwischen mehrmals Spionagesoftware auf die iPhones ihrer Opfer laden. Wie Sicherheitsexperten von Microsoft und Citizen Lab herausgefunden haben, handelt es sich dabei um einen sogenannten Zero-Click-Exploit. Die Malware wird dabei installiert, ohne dass das Opfer auf einen Link klicken oder Rechte freigeben muss. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Apple has backported security patches addressing a remotely exploitable zero-day vulnerability to older iPhones and iPads.
This bug is tracked as CVE-2022-42856, and it stems from a type confusion weakness in Apple's Webkit web browser browsing engine.
Apple said that the flaw discovered by Clément Lecigne of Google's Threat Analysis Group allows maliciously crafted webpages to perform arbitrary code execution (and likely gain access to sensitive information) on vulnerable devices. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
La vulnérabilité Achilles, découverte par Microsoft, a été comblée par Apple dans les récentes mises à jour de macOS Ventura, Monterey et Big Sur.
Enregistrée dans la National Vulnerability Database sous la référence CVE-2022-42821, la faille Achilles a été découverte par Microsoft en juillet dernier. (crédit : Microsoft)
Ceux qui n’ont pas mis à jour leur ordinateur Mac avec la dernière version de Ventura, Monterey ou Big Sur, devraient se dépêcher de le faire. En effet, un méchant bug découvert par Microsoft et corrigé dans les mises à jour livrées par Apple la semaine dernière pourrait être utilisé par un attaquant pour contourner les protections de sécurité strictes du constructeur et installer des logiciels malveillants sur les ordinateurs Mac.
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
App developers and security researchers Tommy Mysk and Talal Haj Bakry from the software company Mysk recently found that iOS sends "every tap you make" to Apple from inside one of the company's own apps. According to the developers, attempts to turn this data collection off, such as selecting the Settings option "disable the sharing of Device Analytics altogether" did not affect the data from being sent. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Apple released emergency security updates to fix two new zero-day vulnerabilities exploited in attacks targeting iPhone and Mac users, for a total of 13 exploited zero-days patched since the start of the year.
"Apple is aware of a report that this issue may have been actively exploited," the company revealed in security advisories describing the security flaws.
The bugs were found in the Image I/O and Wallet frameworks and are tracked as CVE-2023-41064 (discovered by Citizen Lab security researchers) and CVE-2023-41061 (discovered by Apple). Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.
MetaStealer, not to be confused with the 'META' info-stealer that saw some popularity last year, is a Go-based malware capable of evading Apple's built-in antivirus tech XProtect, targeting business users. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
A security researcher caused something of a kerfuffle during the Def Con 2023 hacking conference in Las Vegas last month. Some attendees with iPhones were shocked to see an Apple pop-up notification asking them to connect to a nearby Apple TV device using their Apple ID credentials. Not least, as some of the hackers on the receiving end of these Bluetooth-powered prompts were running with Bluetooth disabled. Or so they thought. Now, another security researcher has demonstrated a similar hack that uses a readily available hacking device to spam nearby iPhones with pop-up notifications and effectively execute a denial of service attack. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Utilisateurs d’un iPhone, d’une tablette ou d’un ordinateur Mac, à vos mises à jour ! Le fabricant Apple vient de publier des correctifs pour ces différents produits, à la suite de la découverte d’une faille (CVE-2023-37450) dans le moteur de navigation WebKit par un chercheur en sécurité anonyme. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
The "rapid" security fixes are designed to quickly patch security flaws under active exploitation by hackers. Apple on Monday released its first batch of publicly available “rapid security” patches, aimed at quickly fixing security vulnerabilities that are under active exploitation or pose significant risks to its customers.
According to a notice, the so-called Rapid Security Response updates “deliver important security improvements between software updates.”
Rapid Security Responses were introduced to allow Apple customers to update their devices faster than a typical software update takes. Apple says the feature is enabled by default, and some rapid patches can be installed without rebooting, though not always. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Last week, we warned about the appearance of two critical zero-day bugs that were patched in the very latest versions of macOS (version 13, also known as Ventura), iOS (version 16), and iPadOS (version 16).
Zero-days, as the name suggests, are security vulnerabilities that were found by attackers, and put to real-life use for cybercriminal purposes, before the Good Guys noticed and came up with a patch. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple’s latest update blast is out, including an extensive range of security patches for all devices that Apple officially supports.
There are fixes for iOS, iPadOS, tvOS and watchOS, along with patches for all three supported flavours of macOS, and even a special update to the firmware in Apple’s super-cool external Studio Display monitor.
Apparently, if you’re running macOS Ventura and you’ve hooked your Mac up to a Studio Display, just updating the Ventura operating system itself isn’t enough to secure you against potential system-level attacks.
According to Apple’s bulletin, a bug in the display screen’s own firmware could be abused by an app running on your Mac “to execute arbitrary code with kernel privileges. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
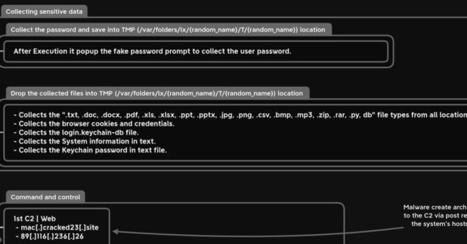
A new information-stealing malware has set its sights on Apple's macOS operating system to siphon sensitive information from compromised devices.
Dubbed MacStealer, it's the latest example of a threat that uses Telegram as a command-and-control (C2) platform to exfiltrate data. It primarily affects devices running macOS versions Catalina and later running on M1 and M2 CPUs.
"MacStealer has the ability to steal documents, cookies from the victim's browser, and login information," Uptycs researchers Shilpesh Trivedi and Pratik Jeware said in a new report. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=MacStealer

|
Scooped by
Gust MEES
|
Apple has just released updates for all supported Macs, and for any mobile devices running the very latest versions of their respective operating systems.
In version number terms:
iPhones and iPads on version 16 go to iOS 16.3.1 and iPadOS 16.3.1 respectively (see HT213635).
Apple Watches on version 9 go to watchOS 9.3.1 (no bulletin).
Macs running Ventura (version 13) go to macOS 13.2.1 (see HT213633).
Macs running Big Sur (version 11) and Monterery (12) get an update dubbed Safari 16.3.1 (see HT213638).
Oh, and tvOS gets an update, too, although Apple’s TV platform confusingly goes to tvOS 16.3.2 (no bulletin). Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Une nouvelle version du malware Dridex cible actuellement les Mac pour se propager sur un grand nombre d'ordinateurs.
Le malware Dridex est déjà connu par les utilisateurs de PC Windows, mais c'est la première fois que ce logiciel malveillant s'attaque à macOS. Pour ce faire, les hackers ont changé le mode de fonctionnement pour parvenir à leurs fins. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
It’s just under a month since iOS 16.1.1 came out for Apple iPhone users, fixing a pair of bugs that were listed with the worrying words “a remote user may be able to cause unexpected app termination or arbitrary code execution”.
Both macOS 13 Ventura and iPadOS got updated at the same time, with a pair of security bulletins published on Apple’s web site.
Now, there’s another security update, apparently moving iPhone users only up to version iOS 16.1.2. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple Is Tracking You Even When Its Own Privacy Settings Say It’s Not, New Research Says
An independent test suggests Apple collects data about you and your phone when its own settings promise to “disable the sharing of Device Analytics altogether.
For all of Apple’s talk about how private your iPhone is, the company vacuums up a lot of data about you. iPhones do have a privacy setting that is supposed to turn off that tracking. According to a new report by independent researchers, though, Apple collects extremely detailed information on you with its own apps even when you turn off tracking, an apparent direct contradiction of Apple’s own description of how the privacy protection works.
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
|






 Your new post is loading...
Your new post is loading...































Major cyber security incidents continue to hit the headlines. Security and privacy are top concerns for IT and security professionals, especially after 2014’s highly publicized data breaches.
Companies around the globe were victim to malware, stolen data and exploited vulnerabilities. Big companies weren’t immune to this, with Target, JPMogan Chase, Home Depot and Sony Pictures suffering the painful sting of data breaches. Even celebrities were targeted, with compromised iCloud accounts.
It really isn’t surprising that almost everyone anticipates the need to prepare for security challenges in the coming months. According to a recent survey by Tech Pro Research, 84 percent of IT professionals are more concerned about security and privacy in 2015.